And why this exploitation allows Jihadists to maintain a persistent information ecosystem.
This is the second in a series of posts that uses data science to sort the anecdotal observation from evidence-based research. After the hype, what about the data? Part 2.
The recent reports of UK government pressure on Automattic and WordPress to remove content posted on Jihadology, has resulted in plenty of opinionated tweets and longer form commentary.
As the UK government has claimed that Jihadology could be used as a convenient platform by extremists, the first past of the post looks at;
- Whether this is a theoretical possibility, or if there is evidence that Jihadology is used by jihadist groups, and if so, how and for what purpose do they use it?
The second part of the post examines whether this is an isolated case;
- is there evidence that individual pieces of Jihadist material which pundits and researchers post on social media and the surface web are subsequently exploited by Jihadist groups.
- Is there evidence that when the aggregated impact of individual tweets and surface web posts are analysed as a collective behaviour, rather than as isolated events, that this creates a resource which is exploited by Jihadist groups – resulting in pundits unwittingly becoming part of the Jihadist information ecosystem?
The evidence shows that Jihadology:
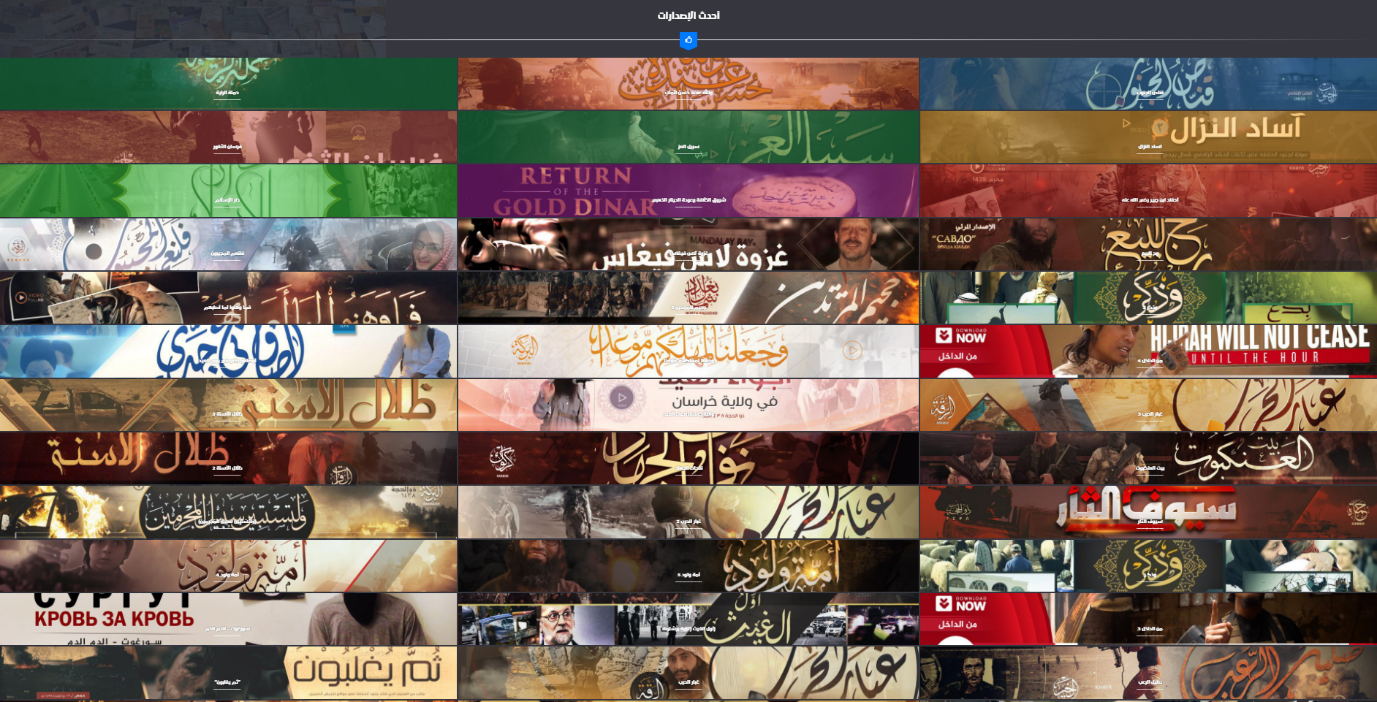
- is used by jihadist groups as a convenient platform through which to share access to videos, and text documents.
- is a source of media to feed JihadistContent Aggregators, allowing material to be shared within a Jihadist context while not being subject to removal.
- is recommended to fellow Jihadist sympathisers as a good place to find content, emphasizing the content on Jihadology does not get banned or removed.
The data further shows:
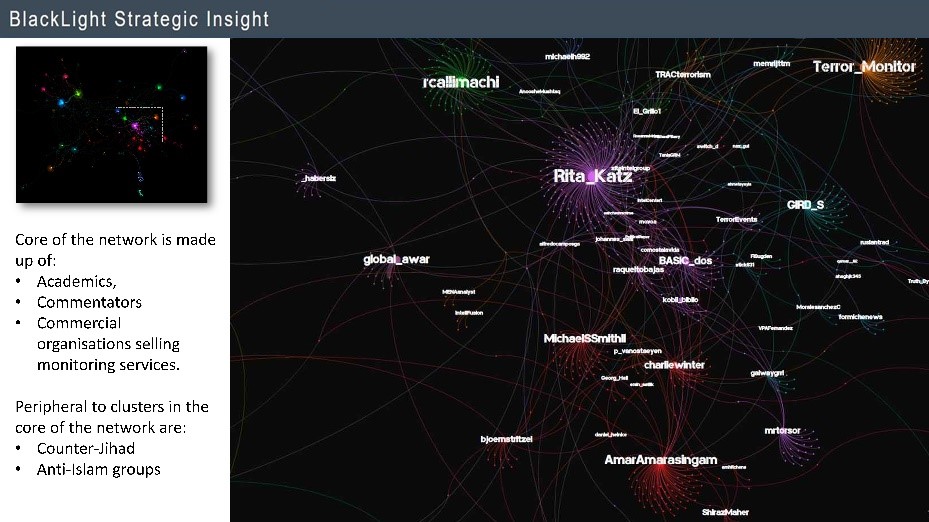
- More broadly, there is a network of researchers and commentators who are publishing Jihadist material on the surface web. The aggregated result of these individual actions is the unwitting creation of an online resource which has been exploited by Jihadist groups and has become part of the Jihadist information ecosystem.
It is perhaps the greatest irony that Government sessions to discuss how to make it harder for Daesh to spread their message online, are often attended by researchers who frequently publish that same content on the surface web and social media.
Introduction
Jihadology describes itself as a ‘clearinghouse’ for jihadi primary source material, original analysis and translation services. As a result, it allows researchers who lack the expertise or experience to find content themselves to publish research.
For those with genuine access, Dawlah al-Islāmiyah, recently released an archive of over 5,200 Media Foundation and Wilayat produced video files (which included multiple language versions of some videos).
They have also followed the tradition of jihadist media groups of releasing numerous astuwanat [barrels / أسطوانات] of content. Each “barrel” contains a collection of material organised by theme, organisation, or specific media production. While previously astuwanat were made available via CD, DVD or ISO file, they are now more often released via torrent or direct download in Telegram – although the banner images promoting them often still contain an image of a disk.
In combination with the ‘Archive’ channels on Telegram, policy professionals and researchers with requisite knowledge, language skills and experience, should be able to access Jihadist material without using Jihadology as a crutch with which they can limp through what should be basic research tasks for those doing more than an undergraduate research essay.
Afterall, given their inability to master the simple task of finding content, it is perhaps unreasonable to expect those leaning on the Jihadology crutch to provide an authentic interpretation of what they find on the site. Furthermore, basing analysis on what is found on the site, leaves the researcher studying what is posted on Jihadology (which is not exhaustive), rather than the range of material extremist groups actually produce.
European Context
The current discussion of Jihadology and pressure on WordPress, occurs within the context of the UK government position that:
“It is reckless to publish terrorist propaganda online without safeguards to stop those vulnerable to radicalisation from seeing it”.
It should perhaps be needless to state that those who are vulnerable to the message of Jihadist groups must as some point become consumers of jihadist material or messages, if they are to be anything other than theoretically vulnerable.
For Jihadist groups da’wa is given via printed material, images, audio, video, speeches, conversations or communicated through specific behaviours. Through this range of delivery methods, individuals are provided with role models and theological guidance for actions, and in which they can use online platforms to gain unfiltered access to the universe of content that is of great importance to jihadist groups.
It is in this context that a report from the UK Parliament’s Intelligence and Security Committee (ISC) criticised social media companies for not acting fast enough to remove content. Furthermore, the FT reported that UK security officials argue Jihadology:
“could be used as a convenient platform for extremists to access videos and messages from outlawed terror groups such as ISIS and al-Qaeda”. (emphasis added).
However, various European countries take different views on what to do about sharing content from groups they deem illegal or extreme. At the time of writing, in France Jihadology is unavailable.
Germany threatens fines for companies not reacting quickly enough to content posted, and the UK imposes prison time for those sharing this content. For example:
- December 2018 – Abdulrahman Alcharbati (diagnosed as bipolar according to the BBC report) was jailed for seven years, for offences including posting ISIS videos on Facebook.
- December 2016 – Abdul Hamid, who Judge Peter Rook QC accepted had ‘significant physical and mental health problems’ was sentenced to two years in prison for posting the video ‘No Respite’.
At this point, in the UK while two men with mental health problems have been sentenced to years in prison for posting ISIS videos, another man is lauded by academics for making the same videos freely available.
This raises important and complex issues as global communication networks exist alongside international borders, and the extent to which Jihadist groups and sympathisers use Jihadology as a platform to access content, and furthermore, the role Jihadology plays within the jihadist information ecosystem.
Reusing individual links
In the New Netwar, we observed that Jihadist groups and their supporters locate individual URL of videos posted on Jihadology and reuse those links within the context of their own channels and groups.

A similar theme was picked up in recently in the Twitter discussion, following the story in the Financial Times, noting it is not just the videopress links (which have previously appeared on Jihadology) but references to the site itself. As @Charlie_KDN noted in a tweet;
Each week 100’s of @Jihadology_Net links are published on ISIS TG chans and groups to rebroadcast suspended content on other platforms.
@Charlie_KDN
For example, links to videos including ‘Honor is in Jihad’ and issues of al-Naba that have been posted on Jihadology are shared on pro-ISIS Telegram channels (as are links to a site run by Pieter van Ostaeyen).

Jihadist Telegram channels re-purposing individual URL from Jihadology
Once the videos are neatly archived by Jihadology – the links are then shared as collections. For example, on a single day in October 70 unique Videopress URL were observed being shared a total of 1,125 times via core Telegram channels.

Jihadist Telegram channels re-purposing individual URL from Jihadology
A potential additional advantage to sharing the Videopress links is that it opens a video player in a web browser, providing a seamless experience for the viewer and ensuring the content is shared in a pro-Jihadist context rather than with a research focus.
Feeding Content Aggregators
In addition to using individual links to content, Jihadist supporters use Jihadology to feed material to their content aggregators. For example, a PasteThis.at link shared in a pro-ISIS Telegram channel, provided a single page from which users could access over 100 issues of al-Naba.

PasteThis.at page re-purposing individual URL for al-Naba up to issue #147 posted on Jihadology
The actual files from which this PasteThis.at page link to were stored on azelin.files.wordpress.com. Using this method Jihadist groups and supporters can provide access to content from within the context of their own discussions, Telegram groups, and theological worldview.
In addition, when Jihadist supporters build individual websites to aggregate content, they have been observed using Jihadology as a source of content. In this example the aggregator was built using Cloud9 which operates as part of Amazon AWS.
The al-Ajnad and al-Furqan options both direct uses to the pages on Jihadology for those entities. Those links have been clicked over 350 and 240 times respectively.

This cloud9 based aggregator also contained a section in which users could select videos by clicking on the banner advertising their chosen video. Many of the links made available in this section were to videopress files, the link for which had previously been shared on Jihadology.
As in the previous example, Jihadology is used to provide a stable source for much of the content. However, the way the site is built a user may be unaware of the actual file location – allowing the aggregator to promote a Jihadist worldview
Why Jihadists use Jihadology:
In addition, to re-using individual links or feeding content aggregators, pro-jihadist or pro-IS Telegram users have been observed posting recommending Jihadology as a source of material. Much of these comments follow a similar theme.
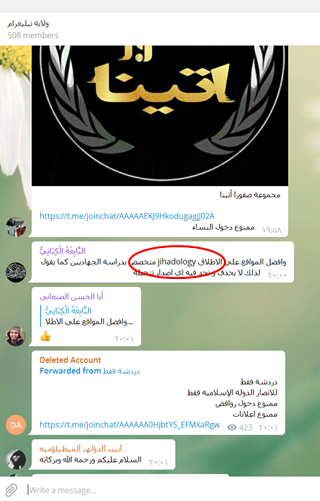
In this example, the Arabic reads.
“and I prefer links to the site jihadology which is specialized in studying jihadists as it states, therefore it neither gets deleted nor any content it hosts gets banned“
Within core IS channels links to the main IS category on jihadology are shared, leading to videos, video series, or the weekly editions of the al-Naba’ magazine:
كامل اعداد صحيفه النبأ من واحد إلى 110 ماعليك الا بالنقر على الرقم وتتحمل. برابط غير قابل للحذف لن يفتح الرابط الا بعد تشغيل ألفي بي ان vpn
#نشر
The text reads:
“All editions of the al-Naba’ magazine, from edition 1 to 110, just change the number in the link and download it. This link will not be deleted and do not open this link without employing a VPN.”
Another message advised:
هنا في هذه الروابط صفحات #لكامل_إصدارات_الدوله_الاسلاميه_من_ولاية_حلب_بروابط_غير_قابله_للحذف
“this site gives you all the links of the releases from wilaya Halab of the Islamic State, the link does not get deleted.”
Conveniently, for the author of this message in a core IS channel, viewers can quickly get the current videos by IS from the province of Aleppo.
It is important to the author of the Telegram message, that while content may be removed elsewhere it is kept in a safe and orderly manner on sites like Jihadology. This allows IS to project their content in an orderly manner, allowing placement of – in this case – geographic located collections to the benefit of ISIS.
This evidence demonstrates it is not that users theoretically “could’ use Jihadology as a convenient platform for extremists to access videos and messages from outlawed terror groups such as ISIS and al-Qaeda” … Jihadists supporters and sympathisers do use it to access individual URL, feed their content aggregators, and recommend it to their peers because the content is not removed. Unfortunately, the recommendation that users adopt VPN to access Jihadology may blunt the efficacy of traffic analysis, a problem which may also be compounded by the many commentators and policy professionals who have recently claimed to be regular users.
This means that while tech and social media companies are pressured, and threatened with fines, the content is still findable and IS supporters and sympathisers know it. As a result, ISIS (and other Jihadist groups) do not have to struggle to maintain a persistent presence for their content online, in addition to using Telegram, they can release the content and then allow sites like Jihadology to archive it for them.
The defence of Jihadology:
In defence of Jihadology, there have been many commentators saying a version of:
“the site is a vital research portal that provides a valuable service for academics, policymakers and journalists researching Islamist extremism”.
There have been numerous researchers who have recently been tweeting that they regularly use Jihadology – effectively announcing they rely on Jihadology as a crutch for their inability to locate or access Jihadist content. Penetrating Jihadist networks (beyond the entry level Nashir type channels) relies on being able to recognise the theologically encoded references and follow the content. As such, one wonders if in future those publicly stating they use Jihadology regularly may reflect on why they consider themselves qualified to conduct the complex task of analysing content when they can’t complete the simple task of locating that content by themselves. The inability to find content, and thereby having to rely on what is posted on Jihadology, may perhaps explain why Arabic language jihadist materials are so rarely referenced or cited in research.
As locating content is a significant part of research production, and given the number of people currently claiming they use Jihadology to find content, it appears Aaron Zelin deservers credit on many more research papers than he is currently recognised as making a significant contribution.
One wonders why commentators on Twitter talk of the valuable contribute made by Aaron and Jihadology, only to reduce that contribution to a reference to jihadology.net in a URL buried in a footnote when that same author publishes their research?
Others steer away from the ‘value’ of the contribution, and instead take the view that the “Content by itself does jack shit”. This follows the rationale that;
“How the message is received and incorporated into a broader worldview and acted upon is one aspect of what we, perhaps too vaguely, call the “process of radicalization”.
This particular researcher visits Jihadology several times a week – one assumes to view content disconnected from “the process of radicalisation” and thereby to study it doing “jack shit” if he follows his own logic, but who knows.
The description of what is broadly an ideational model of behaviour change highlights wider factors in the process. Nobody lives in a vacuum, but ideational models still require an idea to fulfil a fundamental role in this type of behaviour change process. As demonstrated above, links are not shared in a vacuum. Jihadist supporters have become adept at accessing the content posted on Jihadology and sharing it via Telegram channels and through Content Aggregators which project and reinforce their theologically driven worldview. It is in this context that potentially vulnerable people may access Jihadist media production. It is naïve to imagine the content posted on Jihadology can only be accessed by visiting Jihadology.net and searching the site for content.
While Jihadology was never intended to be a platform for jihadist groups, the data shows Jihadology has become a repository for video and written material exploited regularly by ISIS / Jihadist supporters and sympathisers. The links to specific videos or collections of material are shared within the context of aggregators or Jihadist Telegram channels, where the meaning of the content is discussed and Jihadology is recommended as a source that can be relied upon as it is not be deleted.
Just Jihadology?
The data show users in Arabic language Telegram channels recommend Jihadology to their peers as a location for them to view or download content. However, is Jihadology an isolated case or is it unfair for European governments to pick on Jihadology and Aaron Zelin specifically? Is this an example of a wider research sub-culture which actively publishes Jihadist content across social media and the surface web?
Wider Research Sub-culture
Rumiyah
To test whether there is evidence that Jihadology is an isolated case, we turn to the releases of the multilingual magazine Rumiyah using the #Rumiyah hashtag. If Jihadology is an isolated case, we would expect the initial release of each edition of the magazine, to be met with a surge of tweets about it on Twitter from ISIS accounts and supporters. The example below shows that the surge of tweets occurred.
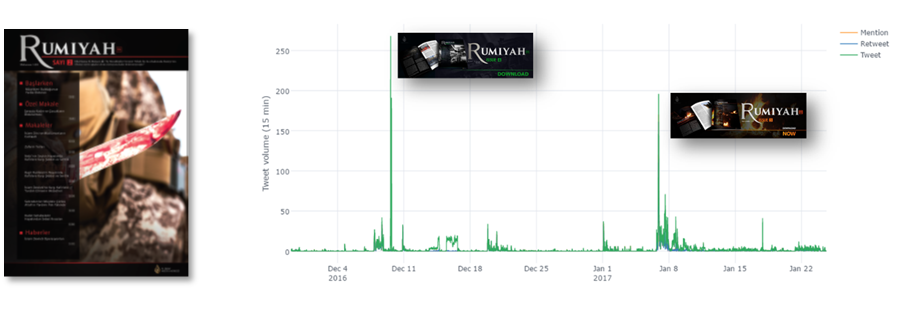
Closer analysis of the data reveals that there are relatively few original tweets, but many retweets. This tends to indicate that there is less emphasis on conversation / interpretation and instead a greater focus on spreading information.
If these spikes were driven by ISIS supporters tweeting until their accounts are suspended one would expect to see many accounts being active for one release and a separate network active for the next release. One would not expect there to be a network infrastructure to span numerous releases. The way this would happen is if accounts were able share news of the release, without being suspended.
To examine nature of the network of retweets (which make up a large proportion of the overall tweets), we used Social Network Analysis (SNA) of the retweets. SNA shows the structure of the network through which news of the magazine release flows. In the case of Rumiyah releases, SNA shows that there was a network of accounts which spans numerous releases.
While Twitter suspends many pro-ISIS accounts, this prominent cluster is able to maintain a persistent presence. A closer examination of this persistent cluster shows it is populated by Academics, Commentators, Reporters and organisations selling monitoring services.
However, are these accounts coincidentally engaged in discussion of the meaning of ‘Rome’ and ‘Romans’ within Jihadist theology, lacking deeper Arabic connectivity, or is this announcing the release of the magazine and / or sharing content from it?
- Note: the coincidental appearance is not as ludicrous as it first sounds. One of the ‘Lend me your ears’ series of videos featuring John Cantlie was released on the same day as an entirely disconnected toga party. Both just happened to use the hashtag #lendmeyourears at the same time. And both ISIS and toga partiers were surprised by the juxtaposition of content.
In reality a review of the tweets shows that this is not coincidental. The network of academics is publishing announcements about the release of the magazine, including the banners ISIS created to promote the release, and sections of the magazine, such as text and graphics.

The sharing of content likely provides greater reach for the content than ISIS could have achieved alone. Reaching as many people as possible was after all one of the main purposes of producing and releasing the magazine, and media material more broadly.
The release of Rumiyah issues was not the only times academics and commentators have probably provided greater reach and longevity for Jihadist content than ISIS could have achieved alone. Looking back over data from recent years, across a range of video announcements, audio releases, and claims of attacks a pattern emerges.
Speeches:
al-Zawahiri – April 2017
In April 2017, al-Qaeda leader al-Zawahiri released a new speech. After an initial tweet by Elizabeth Kendall, covering the key points from the speech @marypgkeating responded posting a link to the speech on YouTube with ‘English subtitles’, while others join in retweeting.

al-Baghdadi
In November 2016, al-Furqan released a speech by al-Baghdadi. The release was greeted by: “Wow – it’s Baghdadi” from Mr Winter, followed by the name of the audio so others could find it and comments on the contents of the speech.

Could this type of tweeting be used to find content? To test this and mimic a ‘naïve searcher’ trying to find content, a search on Google.co.uk in May 2017 (six months later) used the title of the speech as tweeted.
In the results,
- an English translation posted by al-Naba on archive.org,
- a swath of other related ISIS documents including an English translation of a speech by the Abu Muhammad al-Adnani; Official spokesman for the Islamic State and
- an ISIS video from the province of Ṭarabulus which had a similar name. That link lead to the video posted on Jihadology.net.
The test shows that this information could lead uninitiated users to access ISIS content. In addition, the data highlights that individual unwitting actions rapidly combine to provide easy access to a range of genuine ISIS content.
Battle footage and executions
Mosul
In addition to speeches, there were numerous ISIS videos of the fighting in Mosul. For example, the image from this video release from Ninewe province, would have allowed those able to read Arabic or Latin characters to search for the title of the video.

The ‘naïve searcher’ test was conducted in May 2017, using google.co.uk with the English title. This returned both the first and second parts of this series. At the time, ten of the top fifteen results provided a link to the video.
The same test in December 2018 still returned the video via Jihadology.net. This despite the same researcher (who now receives funding from Facebook) giving a bullish claim about the difficulty of finding IS content on social media and surface web.
He recently claimed;
“It isn’t just a case of googling “IS propaganda” and seeing what comes up (any more). This stuff isn’t readily available on the surface web like it used to be. If you’re not on Telegram or in a forum, the options are increasingly limited.”
Beyond the parochialism and evident Western habitus which leads a researcher to imagine the go-to search terms used by Jihadist supporters would include the word ‘Propaganda’, he is also apparently oblivious to the evidence that is available to anyone who bothered to do even the simplest research.
Just putting the content of one of his own tweets into a search engine delivers … IS propaganda. His assurances sound bold, but like many others that circulate within the field, it could not be considered “research-based in any rigorous sense” to use Alex Schmid’s phrase. That is “a very polite, typically academic way of putting it”, Nafeez Ahmed would likely suggest another.
Just like the previous insistence on media ‘decline’, fully fledged collapse, content production correlated to territory, and the ‘naïve notion’ of Utopia, claims about the findability of content have joined the list of claims which have turned out to be, as Rüdiger Lohlker recently highlighted, “an empty fog of words without inner content”. Quoting German philosopher G. W. F. Hegel, the section quoted by Rüdiger Lohlker continues:
This sort of chatter, though lacking the idea of philosophy, gains for itself a kind of authority through its very prolixity and arrogance. Partly this is because it seems almost incredible that such a big shell should be without a kernel…
G. W. F. Hegel
While those at institutions with links to Facebook insist content is hard to find, the actions of ‘experts’ who publish Jihadist content enable even uninitiated individuals to locate the content about the fighting in Iraq and Syria (and elsewhere). In this particular case, the publishing of announcements, pictures, statements and other ISIS material was not an isolated to a couple of examples. The Twitter timeline documented here shows the extent to which publishing of ISIS content made widely available.
Attacks
Responsibility and da’wa
One of the ways in which terrorist groups, of almost all types, have sought to extend their influence, is through claiming responsibility for attacks. Announcing attacks and recognising those responsible for them is important for ISIS and the Jihadist movement. As Abu Mus’ab al-Suri wrote in his Call for a Global Islamic Resistance;
The issue of individual jihad was a great da’wah success. It had great influence on awakening the spirit of jihad and resistance within the ummah, and it transformed unknown individuals such as al Diqamsa, Salman Khatir, Sayyid Nusayr and Ramzi Yusuf into becoming symbols of a nation. The crowds cheer their names, people’s thirst for revenge is satisfied, and a generation of youth dedicated to the Resistance follow their example
Similarly, Anwar al-Awlaki explained (while discussing the seventh meaning of victory);
Prevail here means the prevailing of their da’wah and not always their battles. They could loose (sic) the battle but their da’wah will achieve victory and be available. Nobody can stop their da’wah. The idea is that it will keep this group strong from generation to generation.
Seventh Meaning of Victory, Yusuf al ‘Uyayree Thawaabit ‘ala darb al Jihad (Constants on the Path of Jihad) Lecture series delivered by Imam Anwar al Awlaki (Quoted as transcribed)
For jihadist groups, statements claiming an attack or detailing a battle are not simple information updates, they are part of da’wa; spreading their theology by retelling the actions of the believers. Afterall, as Abdullah Azzam argued, “Jihad is da’wah with a force”.
Following the 2017 attack on the Manchester Arena ISIS issued statements in Arabic and English. A review of data from the time shows a range of researchers, including those based in the UK, either tweeted or retweeted the actual announcement, with collectively 100 retweets of just the four versions identified below.

A snapshot from Twitter on the day following the attack at the Manchester Arena, finds the OSCE held the World Counter Terrorism Conference in Vienna. The conference included discussion of how to make it harder for terrorist groups to spread their message, while some of those at the event were also publishing ISIS content on social media.

One of the attendees tweeted;
- about the OSCE event,
- the OSCE response to the attack in Manchester,
- republished the ISIS claim of the attack,
- before returning to the content of the OSCE event.
The tweeting of announcements was not a single ephemeral event, claims of responsibility were also shared for the attack on the Champs Elysees.

This has also continued in 2019, the current Director of ICSR published ISIS claims of responsibility for the bombing which killed US personnel in Manbij, Syria

The tweeting of this material from Rumiyah to speeches, videos and announcements, has the potential to increase the reach of Jihadist messages. In addition, as shown with the reuse of links to content on Jihadology, Jihadist supporters can also reuse that URL for their own purposes. In the example below from January 2019, an account with a username referencing ISIS responds to a story of Troop withdrawal by posting a link to a section of an ISIS video.

Among the numerous notable elements:
- this specific clip from an ISIS video has 35,600 views on Twitter, despite claims by researchers this material is difficult to find (for them).
- the original video clip was not posted by an ISIS, or Jihadist, account. It was an OSINT focused account, which a supporter subsequently used. This is one of the ways in which Jihadist groups exploit content sharing by commentators and pundits.
What this indicates is an increasingly sophisticated approach in which a user can create a seemingly pro-ISIS account, find a version of an ISIS video posted by an OSINT commentator and subsequently exploit the reticence of Twitter to remove such content from non-jihadist accounts by reposting the URL to the tweet containing the video.
An approach fit for a 21st Century Sisyphus, Yes Minister or Monty Python
Tech companies are understandably reticent to remove content published by researchers. Yet while European governments pressure social media companies to remove content, and try to create upload filters and image hash databases etc. European governments are also giving things of value (salaries, grants, travel, and hotels) to researchers who publish this same material on social media.
As a result, while CTIRU, EUROPOL, Twitter and social media companies more broadly were making efforts to reduce circulation of ISIS content on social media – academics and for-profit organisations publish and republish jihadist content on the same social media platforms, and to an audience beyond that which ISIS could achieve alone.
It is perhaps the greatest irony that Government sessions to discuss how to make it harder for Daesh to spread their message online, are attended by researchers who frequently publish that same content on the surface web and social media.
It is an approach fit for Yes Minister, Monty Python or a 21st Century Sisyphus.
Why this matters to Jihadist groups:
First the evidence above shows that jihadist groups recognise the opportunity to give da’wa by aggregating links to content posted by pundits and researchers. Second, when Western organisations and pundits immediately repost jihadist content, this is then re-posted in pro-ISIS Telegram channels and used to galvanize the mujahid vanguard.
Third, part of their theological understanding of da’wa is to spread their message as widely as possible. This goal of broad dissemination is considered successful if others hear the message of their theology. This has been covered in numerous documents written by a range of leaders of the jihadist movement. These documents have emphasized that spreading their theology as widely as possible is an important component of jihadist activity.
For example, Yusuf al-‘Uyairi recorded in his Constants on The Path of Jihad,
- Jihad will continue until the Day of Judgment (or as referenced in numerous ISIS videos, ‘Until the final hour’), which also connects it to Sahih Muslim / Book 41 / Hadith 6924
- Jihad is not dependent on a particular land, but Jihad must be part of your life,
- Seventh meaning of victory: victory of your idea (Anwar al-Awlaki’s translation is quoted above)
Viewed collectively, in the context they are used by Yusuf al-‘Uyairi, these points recognised that there will always be people to reach, both those to fight and those to give da’wa. Therefore, spreading the message is a constant for the Jihadist movement.
The importance of this task was also covered by ibn Nuhaas, who highlighted the The Virtues of Encouraging Jihad. He quotes Surah al Nisa 84,
“So fight, [O Muhammad], in the cause of Allah; you are not held responsible except for yourself. And encourage the believers [to join you] that perhaps Allah will restrain the might of those who disbelieve. And Allah is greater in might and stronger in punishment.”
Surah al Nisa 84
The phrase “you are not held responsible except for yourself” is interpreted by Jihadists within the context of da’wa to mean that they will be individually judged on whether the individual sought to spread the word, not on whether those who heard that message subsequently responded. Therefore, their interpretation of the duty is to find ways to spread their theology. The purpose of the da’wa effort was also noted by Ayman al-Zawahiri. In his General Guidelines for Jihad, (as-Sahab media) there were two elements to the communication or media work.
First: Educating and cultivating the Mujahid vanguard, which shoulders, and will continue to shoulder, with the permission of Allah, the responsibility of confronting the Crusaders and their proxies, until the Caliphate is established.
Second: Creating awareness within the masses, inciting them, and exerting efforts to mobilize them so that they revolt against their rulers and join the side of Islam and those working for its cause
In more specific guidance he wrote:
Focus on spreading awareness amongst the general public so as to mobilize it. Similarly, focus on spreading a greater level of awareness and understanding amongst the Mujahid vanguard to create an organized, united, ideological, and aware Jihadi force that strongly believes in the Islamic faith, adheres to its rulings, shows humbleness to the believers and deals with the disbelievers with firmness. At the same time, full effort should be put in immediately to ensure that people with scholarly and propagational abilities come forth from within the ranks of the Mujahideen so that our message & belief set may be preserved and the call to Jihad may be spread amongst Muslims.
Researchers publishing the announcements are, in the eyes of jihadist groups who produced the original statements, spreading the da’wa which these acts were intended to give.
In the jihadists mindset, these researchers are tools for their divine mission. The reposting of links to Jihadology clearly indicates the Jihadist mindset on the issue – these are not two separate worlds but one interconnected ecosystem, however unwitting some of the participants are within it.
Why Pick on Aaron?
The data on content releases, from magazines to speeches, to videos and announcement of attacks, shows that Jihadology is not alone in publishing Jihadist content.
The data analysis shows a research sub-culture has developed in which posting jihadist content on social media is an acceptable norm; Aaron Zelin is just one part of a much wider network of researchers publishing ISIS and jihadist content on social media and surface web.
Given the extent to which publishing jihadist content on social media and the surface web has become a norm for pundits who make up this research sub-culture, it seems both unfair and entirely ineffective for European governments to target Jihadology and Aaron Zelin as if he and his website are an aberration distinct from the research sub-culture of which he is part.
To what extent can European governments threaten social media companies with fines (or individuals with prison time), when those same governments work with, give things of value to, or employ the researchers and commentators who post that same content on the same social media platforms?
Ethical approaches and leadership.
The kneejerk censorship vs. academic freedom arguments move nothing forward. It merely provides more time for Jihadist groups to distribute their material by exploiting the current way .
Researchers who publish ISIS theologically driven content (and almost invariably without real analysis) often claim to offer these materials to a wider audience for the ‘greater good’. The evidence shows, they are complacently enabling the jihadist movement to remain a coherent online presence – a situation inevitably to the advantage of the movement.
Years ago, when I had the privilege of working on a project with researchers at CEOP, their professionalism, integrity and approach eclipsed that which currently passes as the norm in what might loosely be termed Terrorism Studies.
They had a robust approach to mental health. Upon finding new material or images of child exploitation they did not franticly tweet them. Upon hearing of an attack, they did not reach for their phone to alert journalists to their availability for interview. Finding indecent images of children on a new platform, they did not begin pitching the story of the ‘next big thing’ to whoever would take it. When serious events caused the issue to make the headlines, they did not use it as a reason rush to the TV studios and tweet about being on TV.
These researchers did not spend any time on how many Twitter followers they had, and they certainly didn’t tweet about how many followers they had. From my limited experience of working with researchers from CEOP, they avoided behaviours that could make the situation worse, that could make the content more widely available, or could exacerbate the suffering of victims. From the evidence above, the study of terrorism is generations behind their example.